LAST WEEK'S RELEASES (13)
КРУГЛЫЙ СТОЛ БЛОКЧЕЙН В РОССИИ: ВЗГЛЯД СКВОЗЬ ПРИЗМУ ПРАКТИКИ
Written by Aleksandr Podobnykh2 апреля 2024 года в журнале Информационная безопасность (в разделе Технологии) были опубликованы материалы круглого стола, в котором принял участие Александра Подобных, главы департамента расследований BitOK, руководителя Санкт-Петербургского РО АРСИБ, руководителя Комитета по безопасности цифровых активов и противодействию мошенничеству, судебный эксперт, на тему — Блокчейн в России: взгляд сквозь призму практики.
Кажется, мы стали забывать, что блокчейн как технология обладает многогранным потенциалом и выходит далеко за рамки криптовалют. Практические российские проекты в этой сфере имеют свои особенности, учитывающие не только специфику предметной области и требования законодательства, но и опыт криптовалютных реализаций блокчейна, как позитивный, так и негативный. Эксперты с практическим опытом в области блокчейнов ответили на вопросы журнала «Информационная безопасность».
Участники:
Артем Калихов, генеральный директор Web3 Tech
Владимир Лазарев, со-основатель АМЛ Крипто
Александр Подобных, глава департамента расследований BitOK
Михаил Чеканов, генеральный директор АО «Промышленные криптосистемы»
Востребованы ли в России решения на основе блокчейнов, но не связанные с криптовалютами и цифровыми финансовыми активами?
Михаил Чеканов, Промышленные криптосистемы:
Безусловно, востребованы. На российском рынке представлены разные отраслевые решения, работающие на технологии распределенного реестра. Пример – наша платформа "Контрактиум" для управления цепочками поставок на базе цифровых контрактов с возможностью подключения финансовых и логистических сервисов.
Самым знаковым проектом для нас стала платформа Smart Fuel, спроектированная и разработанная в интересах компании "Газпром нефть". Решение переводит в цифру все операции, связанные с заправкой самолетов, от согласования цен и заказов до формирования отчетов в ФНС и взаиморасчетов через традиционную банковскую инфраструктуру.
Владимир Лазарев, АМЛ Крипто:
В России наблюдается высокий интерес к блокчейн-решениям. Технологии распределенного реестра применяются в различных сферах для повышения прозрачности, безопасности и эффективности бизнес-процессов. Особенно перспективными являются проекты, использующие смарт-контракты и NFT для надежного хранения данных и автоматизации действий.
Развитие этих технологий поддерживается как крупными предприятиями, так и государственными структурами, активно исследующими возможности блокчейна для оптимизации своих процессов. Мы в AML Crypto используем блокчейн для записи данных о результате проверки пользователем того или иного блокчейн-адреса. Это позволяет доказать факт должной осмотрительности при работе с внешними контрагентами.
Артем Калихов, Web3 Tech:
Да, востребованы. Ряд наших крупных блокчейн-проектов вообще не связан с ЦФА. Например, цифровая платформа распределенного реестра ФНС эффективно реализует взаимодействие государственных ведомств и финансовых организаций.
Федеральная блокчейн-платформа ДЭГ 2020 г. успешно используется избирателями по всей стране в единые дни голосования. Растет интерес к решениям для реорганизации трансграничных платежей, благодаря блокчейну здесь возможно множество вариантов реализации.
Александр Подобных, BitOK:
Да. Например, сервис ЕДРИД (Единый депозитарий результатов интеллектуальной деятельности), который работает уже более шести лет и позволяет оформить авторское право.
В онлайн-сервисе писатели, программисты, дизайнеры, фотографы, музыканты и ученые могут защитить свое авторское произведение (разместить на хранение электронную версию произведения) и получить документ в виде бумажного авторского свидетельства с несколькими степенями защиты.
В чем основные практические преимущества решений на основе блокчейна по сравнению с традиционной архитектурой?
Артем Калихов, Web3 Tech:
1. Блокчейн обеспечивает неизменность данных за счет своей архитектуры без необходимости дополнительных средств защиты.
2. В отличие от централизованной инфраструктуры, в рамках экосистемных проектов стоимость интеграции новых участников не растет экспоненциально.
3. Будучи распределенной системой, блокчейн обеспечивает отказоустойчивость, недоступную централизованным решениям.
4. Благодаря смарт-контрактам блокчейн позволяет просто автоматизировать различные договорные и транзакционные процессы.
Александр Подобных, BitOK:
1. Надежная защита на уровне криптографии (депонирование в электронном депозитарии подтверждает существование в определенный момент времени произведения при помощи цифровой подписи, электронного штампа времени и хеш-кода депонирования).
2. Быстрый и оптимальный по стоимости способ фиксации объекта прав (первым в мире реализовал способ фиксации времени депонирования авторского произведения в распределенном реестре).
3. Быстрый поиск аналогов по российским и иностранным базам при регистрации объекта авторских прав (и дальнейшая защита в соответствии с российским и международным законодательством).
4. К примеру, регистрация одного произведения заняла у меня один час и стоила 1200 руб. На следующий день уже поступило свидетельство на электронную почту (в Роспатенте рассматривают 2–3 месяца и стоит 25 тыс. руб.).
Михаил Чеканов, Промышленные криптосистемы:
1. Математически гарантированное доверие к результатам совместной работы без необходимости в централизованном сервисе (базе данных). Традиционный же подход подразумевает наличие посредника, который всегда создает риски для других участников рынка.
2. Затраты на внедрение и сопровождение сопоставимы c традиционными решениями, а возможности развития и скорость реакции на изменения на основе блокчейна – гораздо выше.
3. Катастрофоустойчивость и доступность. Распределенная архитектура обеспечивает бесперебойное обслуживание сделок, главное, чтобы контрагенты были доступны. То есть каждый участник сам обеспечивает нужный ему SLA.
Владимир Лазарев, АМЛ Крипто:
Блокчейн обеспечивает прозрачность за счет неизменяемости записей, доступных всем участникам. Это усиливает безопасность, защищая данные криптографией и снижая риск мошенничества. Снижение затрат достигается за счет автоматизации и исключения посредников. Блокчейн повышает эффективность, ускоряя транзакции и процессы. Децентрализация снижает риски коррупции, увеличивая доверие.
Но важно отметить, что:
- преимущества блокчейна не всегда реализуются автоматически;
- для достижения желаемых результатов требуется тщательное планирование и реализация;
- блокчейн не является универсальным решением и подходит не для всех задач.
Есть ли технологические особенности реализации систем на основе блокчейна в России?
Владимир Лазарев, АМЛ Крипто:
В России реализация блокчейн-систем имеет свои технологические особенности: строгие нормативные требования, необходимость интеграции с устаревшими системами, высокие стандарты кибербезопасности на фоне геополитической ситуации, политика импортозамещения требует отечественных ИТ-разработок.
Ключевыми факторами являются: кадровый дефицит в области блокчейна, ограничения на использование криптовалют, требования к масштабируемости и энергоэффективности, а также необходимость обеспечения конфиденциальности данных. Кроме того, важно учитывать юридические аспекты, связанные с новизной технологии. При тщательном планировании и реализации блокчейн может стать мощным инструментом для развития различных сфер российской экономики.
Артем Калихов, Web3 Tech:
Технологические особенности реализации блокчейн-систем в России связаны в первую очередь с регуляторной политикой в отношении средств криптографии. Для информационных систем здесь предусмотрен список ГОСТов, охватывающий множество направлений – хеширование, контроль целостности и не только.
Этим требованиям пока соответствуют лишь единичные решения на рынке, в том числе наша платформа "Конфидент", имеющая сертификацию средства криптографической защиты информации КС2.
Александр Подобных, BitOK:
Если говорить об операторах выпуска или обмена ЦФА (регулирует деятельность которых Банк России), то, скорее всего, речь будет идти о приватных (частных) блокчейнах. А так как для финансового сектора есть жесткие требования по защите информации, то потребуется и отечественная криптография.
Михаил Чеканов, Промышленные криптосистемы:
Отечественный рынок выдвигает два основных требования:
- обеспечение юридической значимости операций;
- надлежащая защита данных.
Одним из критичных факторов для большинства заказчиков на нашем рынке является поддержка сертифицированных СКЗИ. Это связано с выросшим уровнем угроз ИБ и ужесточением государственного регулирования. В нашем случае эта задача решена путем встраивания сертифицированных средств криптозащиты линейки ViPNet.
Какие технологические возможности стоит учесть в российских системах, с учетом опыта криптовалютных блокчейнов, каких ошибок лучше избежать?
Артем Калихов, Web3 Tech:
Стоит отметить, что в подавляющем большинстве российских проектов используются приватные блокчейны, а не публичные протоколы, применяющиеся для криптовалют. Они обладают другой моделью безопасности. Особое внимание, как правило, стоит уделять безопасности смарт-контрактов, архитектуре блокчейн-решений, криптографии, защищенности и конфиденциальности данных.
Михаил Чеканов, Промышленные криптосистемы:
Лучшее решение – это избегать одноранговых платформ, выросших из криптовалютных блокчейнов. Они плохо интегрируются с реальным ИТ-ландшафтом, инфраструктурой безопасности и здравым смыслом.
Александр Подобных, BitOK:
Многие проекты в нашей стране начинались из открытых проектов или путем создания форков (новых веток). Важно купировать выявленные за это время уязвимости и учитывать наработки сообщества по совершенствованию алгоритмов этих блокчейнов.
Необходимо соблюдать баланс между уровнем децентрализации и анонимностью. Не нужно забывать про формирование единой экосистемы и унификацию блокчейнов и смарт-контрактов, обращать внимание на формирование инновационной культуры и спроса на инновационную деятельность.
Владимир Лазарев, АМЛ Крипто:
При разработке блокчейнсистем в России стоит учесть опыт криптовалютных блокчейнов, особенно в вопросах масштабируемости, конфиденциальности и регулирования. Важно выбирать технологии, обеспечивающие высокую пропускную способность и анонимность транзакций и при этом соответствующие законодательству.
Необходимо обеспечить безопасность и прозрачность, а также гладкую интеграцию с существующими системами, придерживаясь при этом законодательных требований. Для успешной реализации проекта критически важно избегать таких ошибок, как выбор неподходящей платформы, недооценка сложности проектов, пренебрежение безопасностью, неготовность к изменениям и игнорирование регулятивных требований.
Как применение блокчейнов увязывается с текущим законодательством?
Александр Подобных, BitOK:
В сфере ЦФА важны локализация и суверенитет. Так, операторы должны использовать продукты из реестра отечественного ПО, российскую криптографию и иметь лицензию ЦБ РФ. На практике мы видим скорее применение частных (но иностранных) блокчейнов с достаточно надежным шифрованием, соответствующим международным стандартам защищенности.
Если говорить о перспективах развития 115-ФЗ и его оптимизации, то необходимо создание единого оператора по KYC/AML, который будет хранить информацию о клиентах и рисках во внутреннем блокчейне (и предоставлять доступ операторам ЦФА и банкам, для которых процедуры слишком ресурсоемки). На сегодняшний день техническая возможность для этого уже есть.
Артем Калихов, Web3 Tech:
Формально использование самих блокчейн-технологий в нашей стране не регулируется. Тем не менее требования законодательства затрагивают целый ряд технологий, необходимых для практического применения блокчейна, – криптографические алгоритмы, TLS, PKI, и не только.
Блокчейн-платформам необходима гибкость, в некотором смысле даже модульность, которая позволит подстраиваться под регуляторные политики – как для ИТ-отрасли в целом, так и для отдельных сфер применения, например для финансового сектора.
Михаил Чеканов, Промышленные криптосистемы:
Грамотно спроектированные прикладные решения на базе распределенных реестров хорошо вписываются в действующее законодательство. На данный момент мы не видим каких-либо непреодолимых барьеров. Отдельные нормы можно было бы оптимизировать, но лучшее – враг хорошего.
Например, ФЗ-259 "О ЦФА" зарегулировал рынок цифровых активов до абсурда. До сих пор непонятно, зачем в нем упомянуты распределенные реестры, если все функции привязаны к централизованной информационной системе оператора (обмена) ЦФА. Примерно с таким же успехом можно было бы "завернуть" Интернет в отдельного оператора связи.
Владимир Лазарев, АМЛ Крипто:
Законодательство может стимулировать развитие блокчейн-технологий и их применение. Но в то же время несвоевременные или недоработанные законы замедляют прогресс.
Эффективное внедрение блокчейн-технологий требует гибких регуляторных рамок, создания множества пилотных зон для стимулирования экспериментов в этой области.
Источник: Информационная безопасность
ЦИФРОВАЯ КРИМИНАЛИСТИКА РАСПРЕДЕЛЁННЫХ РЕЕСТРОВ
Written by Aleksandr PodobnykhКоллеги, 27 марта текущего года, на ЛитРес вышла наша первая методичка для силовиков, экспертов, специалистов и регуляторов - Цифровая криминалистика распределённых реестров.
Упор сделан на блокчейн Биткойна и сопутствующие технологии, но и коснулись других виртуальных валют и цифровых финансовых активов. В приложении описан примерный алгоритм исследования криптоадресов и транзакций в блокчейнах.
Основные разделы:
- термины и определения
- история появления биткоина
- как работает блокчейн Bitcoin
- криптовалюта как высокорисковый ресурс
- майнинг-пулы
- криптокошельки
- сервисы аналитики рынка цифровых активов
- судебная практика в РФ
- заключение и перспективы развития
Методические рекомендации внесены в особый реестр, что позволяет использовать их в судебно-экспертной и научно-исследовательской деятельности.
Спешите приобрести и поддержать дальнейшие исследования отечественных ученых, по данному направлению ;)
Читать: на ЛитРес
ИТОГИ ЛЕТНЕЙ ШКОЛЫ CTF 2023 И БЛАГОДАРНОСТИ
Written by Aleksandr Podobnykh30 Июля 2023 года в одиннадцатый раз открыла свои двери для слушателей Летняя Школа CTF – высококлассный интенсив по информационной безопасности от лучших в своём деле! В этом году среди слушателей и гостей были не только наши соотечественники, но и представители международного CTF-сообщества.
Топовые спикеры ведущих российских компаний выступили с более чем 30-ю докладами, донося до аудитории последние тренды и самую актуальную информацию из мира информационной безопасности. Не забыли организаторы и о смежных сферах, которые могли бы помочь ребятам на пути становления в качестве защитника информации.
Полное погружение в тему, развитие уже имеющихся и овладение новыми навыками, активный отдых и практические задания, а также тренинги, мастер-классы, Хакатон, технические лабораторные и развлекательная программа – всё это ждало 77 слушателей одиннадцатой летней смены, 26 из которых попали на интенсив совершенно бесплатно, благодаря грантам от наших партнёров.
Мероприятие проводилось при поддержке НАМИБ, Минцифры России и Губернатора Московской области.
Первым делом! Формирование команд
Открыл неделю командный этап хак-квеста, который представляет собой не только отличную возможность впервые проявить себя, но и познакомиться с другими слушателями ЛШ, выполняя общие задачи.
Первая часть квеста была больше нацелена именно на знакомство ребят друг с другом: участникам предлагались простые задания, основной целью которых являлась работа в команде, сплочение коллектива и знакомство с территорией (пройтись вместе по натянутой веревке, передать информацию посредством пантомимы и т.д.)
На втором этапе ребятам уже было необходимо научиться ориентироваться на местности и при помощи мобильных устройств решать CTF-задачки, уровень сложности которых постепенно возрастал.
Таким образом, уже на самом старте участники могли понять свои сильные и слабые стороны, а организаторы, внимательно следившие за ходом мероприятия, в свою очередь, подсказать оптимальные пути решения возникших проблем.
Основываясь на достижениях, манере поведения и особенностях освоения этапов хак-квеста, а также по результатам прохождения тестирования, состоявшегося ещё до старта Летней Школы, были сформированы 11 команд, во главе которых были поставлены индивидуальные кураторы.
Практическая часть
Практическая часть Летней Школы CTF состояла из ежедневных задач, интенсивов, мастер классов и лабораторных работ, в число которых входили:
1) Таск дня – выдавались участникам ровно на 24 часа, по истечении отведённого времени сдать их было нельзя. Сами таски охватывали широкий спектр CTF-задач:
· OSINT;
· элементы Социальной Инженерии;
· креативные задачи;
· задачи на внимательность и так далее.
2) Умный Дом – ряд задач, при решении которых не было привычного флага, но происходили какие-либо физические действия - отключение света/системы вентиляции, включение электрической дуги или насоса для перекачки жидкости, открытие электронного замка и т.п.
3) 36-часовой Хакатон для всех команд – в этом году в качестве задания участникам было предложено «доработать» действующего бота ЛШ или предложить новые интересные задумки для него. Сложность была в том, что сперва было необходимо разобраться в действующем коде, а уже потом делать свою прослойку.
4) AntiCTF – разработка собственных заданий в формате CTF и последующая четырёхчасовая игра среди команд.
5) LastCTF – AntiCTF от участников прошлой ЛШ.
6) Проведение лабораторных работ по Attack-Defence.
7) Лабораторная работа по сетевому администрированию VSFI.
8) Тематическое задание «Танк» – участникам необходимо было разобраться с действующей конфигурацией танка и написать собственную прошивку, а также сделать электронную подпись к ней, залить всё в предоставленный гитлаб и успешно пройти CI/CD проверки.
9) Классический FlappyBird, но в усложненной конструкции - в этом году требовалось быстро и точно нажимать определенные клавиши, чтобы птичка летела.
10) Мастер-класс по Security Operation Center (SOC) – расследование реального инцидента и восстановление событий по цепочке логов.
11) WAF ByPass – задача на обход фильтров WAF по разным векторам.
12) Дополнительные таски по различным категориям - криптография, веб-уязвимости, ppc.
13) Отдельное новшество этой ЛШ - новое командное задание на распайку различных конструкций. В зависимости от уровня сложности (робот, светодиодный куб, металлодетектор и т.д.) команде выдавался набор для самостоятельной сборки (DIY) определенного типа. Задачей было полностью распаять данную конструкцию и продемонстрировать ее работоспособность.
14) Задание на построение модели системы защиты облачного сервиса - задача от нашего партнера Координационного Центра РФ.
За решение практических заданий участники получали баллы в два зачета: командный и индивидуальный. На закрытии Летней школы те, кто набрал наибольшее количество баллов, получили подарки от наших партнеров.
Победители:
Личный зачет 1 место - Световой Владислав
Личный зачет 2 место - Пахомов Глеб
Личный зачет 3 место - Черкасов Евгений
Командный зачет 1 место – Slammer
Командный зачет 2 место – Nimbda
Командный зачет 3 место - Enigma
Спикеры, лекции, семинары
Каждый год мы стремимся дать слушателям Летней Школы самую полную и актуальную информацию по всем направлениям, для чего приглашаем топовых экспертов отрасли, готовых поделиться с новым поколением безопасников бесценным опытом становления и активной работы в сфере информационной безопасности.
Мастер-класс «Коммуникация» (Татьяна Ширяева, Виктор Минин) и тренинг по профайлингу от Даниила Лобанова помогли ребятам лучше понять алгоритмы работы в команде, прокачать коммуникационные и социальные навыки, необходимые для создания любой успешной команды. Ведь CTF – это в первую очередь коллектив, общение и решение конфликтов в котором являются залогом долгой и продуктивной работы.
Буквально за неделю до старта Летней Школы с Северного Полюса вернулся наш бессменный спикер, «любимый разведчик Кремля» и ведущий эксперт по конкурентной разведке Андрей Масалович, известный также под псевдонимом КиберДед.
В свои 62 года Андрей Игоревич способен зарядить энергией небольшую электростанцию, является гвоздём программы крупнейшей российской конференции Positive Hack Days и, несмотря на санкции, наложенные на него в этом году, за «продажу инструмента для слежки на базе больших данных», обретает всё большую популярность в среде как совсем юных, так и опытных безопасников, чему, помимо прочего, способствовал и выход книги «Кибердед знает».
Разработанная им система интернет-разведки Avalanche, ставшая предметом яростных дебатов в сети не только в России, но и далеко за её пределами, уже более 10 лет успешно справляется с поставленными задачами.
Слушателям Летней Школы посчастливилось из первых уст получить информацию о том, как извлекать информацию из больших баз данных и гаджетов, из невидимого интернета и интернета вещей. Такой навык становится особенно полезным в турбулентные времена. Сегодня OSINT (Open Source INTelligence - разведка по открытым источникам) это не просто сбор информации о конкретных объектах интереса, а инструмент выживания и процветания.
В докладе рассматривались более двадцати новых приемов и инструментов интернет-разведки. Приятным бонусом стала подаренная всем участникам интенсива книга Андрея Игоревича с персональным автографом.
Пообщался со слушателями Летней Школы и Мустафин Ильназ – руководитель направления безопасной разработки компании Киберпротект, начавший свой путь в IT более 10 лет назад с Service Desk. Ильназ представил доклад на тему «Безопасный код: вселенная без "черных дыр"», в котором рассказал о:
- принципах secure by design;
- безопасном коде и том, каким тот должен быть;
- как выстроить процесс SSDLC (Безопасная разработка);
- для чего нужны DevSecOps в SSDLC;
- поиски "черных дыр", перед релизом.
Отдельно хотелось бы отметить, что компания Киберпротект выступила спонсором гранта, благодаря чему на безвозмездной основе на ЛШ2023 смог попасть ещё один одарённый участник!
Уже который год подряд мы были рады приветствовать в стенах Летней Школы Дмитрия Склярова - ведущего аналитика Positive Technologies, руководителя отдела исследования приложений, доцента кафедры информационной безопасности МГТУ и автора книги «Искусство защиты и взлома информации». Дмитрий занимается анализом двоичного кода, недокументированных протоколов и структур данных.
Участники интенсива с большим интересом прослушали доклад эксперта «Я реверсер, я так вижу!», в рамках которого эксперт поделился своим опытом и взглядами на причины проблем с кодом и процессы, которые эти проблемы призваны ликвидировать.
Организаторы сердечно благодарят всех спикеров, выкроивших в своём рабочем графике время, чтобы посетить Летнюю Школу CTF и пообщаться со слушателями интенсива! Каждому хочется выразить слова благодарности, каждого отметить. Именно благодаря вам растёт новое поколение заинтересованных, мотивированных безопасников, способных обеспечить достойную защиту данных, и по-настоящему увлечённых своим делом специалистов!
Особые гости
Летнюю Школу CTF 2023 посетили и особые гости. И первым делом мы бы хотели рассказать о выдающейся личности, полковнике в отставке, разведчице-нелегале Людмиле Ивановне Нуйкиной!
Вместе с мужем она до 1986 года работала в более чем 18 странах мира. Успешно решала большой комплекс стоящих перед разведкой задач. Разведчики-нелегалы трудились в государствах с жестким административно-полицейским режимом в условиях, сопряженных с риском для жизни. Мужественно преодолевали все трудности.
Активная оперативная деятельность супругов была нацелена на добывание сведений экономического, военно-политического и научно- технического характера, а также на ведение поисковой работы среди представляющего интерес вербовочного контингента. Людмила Ивановна лично участвовала в обеспечении и успешном проведении ряда ответственных оперативных мероприятий.
Рады сообщить, что совсем скоро выйдет видеоинтервью с участием этого знакового для нашей разведки человека, которое будет опубликовано в ВК-группе Летней Школы CTF!
Прекрасной возможностью больше узнать об истории CTF, услышать о взлётах и падениях региональных соревнований и в целом проникнуться атмосферой нашего CTF-комьюнити воспользовались преподаватели самых разных вузов:
· ТюмГУ
· СурГУ
· ИТМО
· Кубанский институт информзащиты
· ПГУТИ
· КИП ФИН
· ННГУ
· Университет МВД им. Кикотя В.Я.
· МЦК-КТИТС
· МУИТ (Казахстан)
Помимо прочего, для уважаемых гостей были проведены отдельные семинары, способствовавшие лучшему пониманию организационных вопросов, связанных с проведением и подготовкой к CTF-соревнованиям. Более опытные коллеги поделились своими наработками относительно того, как встроить обучение и тренировки в образовательный процесс, чтобы не перегрузить учебный план. Говорили о трудностях, с которыми могут столкнуться организаторы и преподаватели и о том, как с ними лучше справляться.
Посетили наш интенсив и гости из Казахстана и Монголии. Ребята всё активнее проявляют себя в CTF-комьюнити и с большим азартом относятся к стоящим перед ними задачам по развитию CTF-движения в своих регионах. В рамках проведения VIКубка CTFРоссии мы уже встречались с талантливыми участниками из казахской команды SCIMUS_VERUM и очень рады были приветствовать новых, искренне заинтересованных темой ИБ ребят на Летней Школе 2023. Делиться опытом с людьми, увлечёнными нашим общим делом – настоящий подарок!
Искренне надеемся, что столь конструктивное общение и обмен опытом посодействуют еще более стремительному развитию CTF-движения как в России, так и за её пределами.
Отдельно хотелось бы отметить выступление исполнительного директора Всероссийского общественного движения наставников детей и молодежи «Наставники России», ведущего аналитика Центра развития и воспитания личности ФГБУ Российской академии образования Андрея Самотоина. В рамках диалога с аудиторией Андрей Николаевич говорил о важности ближайшего окружения любого человека, особенно только начинающего свой путь становления и личностного роста.
Также на гостевой основе присутствовали и ребята, только начинающие интересоваться темой ИБ. Впечатлённые той атмосферой и пользой, которыми пропитан наш интенсив, они серьёзно занялись самоподготовкой и готовятся присоединиться к слушателям Летней Школы в следующем году!
Развлекательная часть
Не забыли организаторы и о том, что на дворе стоит прекрасная погода, а качественный отдых лишь способствует лучшему усвоению материала! Мы приложили максимум усилий, чтобы обучение ребят проходило в комфортной среде, создавали условия не только для получения знаний, но и общения, налаживания связей; проводили «Угадай мелодию», «Что? Где? Когда?», дискотеку, караоке, спортивные игры, «Киллера», фестиваль красок холи и многое другое.
Очень «душевным и тёплым» мероприятием, по словам самих участников, получилось неофициальное закрытие летней смены 2023: после высказанных организаторам слов благодарности, был зажжён огромный костёр, рядом с которым все могли поучаствовать в «Обнимашках» и повязать друг другу ниточку на память, сопроводив ту тёплыми словами и пожеланиями.
Отмечать день флага Российской Федерации стало уже доброй традицией. Каждый год на Летней Школе мы заранее празднуем этот день и в этот раз он прошёл не менее ярко, чем в предыдущие, завершившись ярким праздником красок холи, так полюбившимся нашим участникам.
Круглый стол АРСИБ
В рамках Летней Школы CTFбыл проведён круглый стол Ассоциации руководителей служб информационной безопасности, главной задачей которого являлось построение доверительной и эффективной коммуникации между ведущими экспертами в области информационной безопасности и аудиторией.
Специалисты делились своим опытом и рассказывали ребятам о входе в профессию, о том, насколько актуальна и востребована на сегодняшний день специальность сотрудника служб информационной безопасности, разбирали кейсы и не упускали возможность разрядить атмосферу парой-тройкой забавных случаев из практики.
12 экспертов – 12 историй становления в профессии – 12 пожеланий и напутствий слушателям ЛШ2023.
География участников
Всего для участия в интенсиве были отобраны 77 участников из России и ближнего зарубежья. Ребята приехали к нам из таких городов, как:
· Алматы
· Воронеж
· Дзержинск, Нижегородская область/ Нижний Новгород
· Ростов-на-Дону
· Донецк
· Екатеринбург
· Зеленоград
· Казань
· Канск
· Котельники
· Красногорск
· Краснодар
· Москва
· Мытищи
· Орел
· Пушкино
· Санкт-Петербург
· Сургут
· Таганрог
· Томск
· Тюмень
· Уфа
Список образовательных организаций:
Школа №618
Школа №152
Школа №179
Школа №31 Санкт-Петербург
Школа "Интеграл"
Школа Космонавтики
Лицей №1580 им Н.Э. Баумана
Лицей №153
Лицей НИУ ВШЭ
Школа "Летово"
Воронежский Государственный Унивеститет
Донецкий Национальный Университет (ДонНУ)
Казанский Федеральный Университет
КИП ФИН
Колледж связи №54
КПК РТУ (МИРЭА)
Краснодарский Университет МВД России
МАИ
МГТУ имени Н.Э. Баумана
Московский Университет МВД им. В.Я. Кикотя
МТУСИ
МУИТ
ННГУ им Н. И Лобачевского
РТУ (МИРЭА)
Санкт-Петербургский университет МВД
СурГУ
ТУСУР
ТюмГУ
Университет ИТМО
УрФУ
ЮФУ
Ithub
Дополнительная информация
LETOCTFBOT
В этом году мы вновь не стали отказываться от предоставления возможности всем желающим попасть на Летнюю Школу совершенно бесплатно! 1 июня был запущен LETOCTFBOT, в рамках взаимодействия с которым ребята могли заранее оценить уровень собственной подготовки и выиграть поездку на летнюю смену, набрав максимальное количество баллов за решение тасков.
Каждую неделю пользователи получали новое задание, на решение которого отводилось 7 дней. По истечении отведённого срока организаторы публиковали верное решение, после чего участники могли продолжить решение таска лишь вне зачёта.
В этом году победителем среди 340 претендентов стала Авдеева Лиза и неудивительно, что именно ей также был выделен грант одним из наших партнёров, а потому решением оргкомитета главный приз перешёл к следующему за Лизой конкурсанту, которым стал Гантумур Золбообаяр из Монголии! Расходы на его проживание, обучение и дорогу полностью взяли на себя организаторы Летней Школы.
Собеседования перед зачислением
Новшеством этого года стало введение личных бесед перед зачислением в ряды слушателей интенсива. Всего было проведено 250 собеседований, по результатам которых зачислены 77 участников.
Место проведения
Летняя Школа CTF – это не только прекрасная возможность прокачать свои знания, но и провести 10 дней в экологически чистой лесопарковой зоне! Каждый год мы тщательно выбираем место для проведения интенсива.
Стараемся учесть всё: удобство расположения, наличие необходимого оборудования и комфортабельных конференц-залов для проведения лекций; следим за питанием и здоровьем наших подопечных. Наличие особенностей развития или патологий здоровья, требующих отдельного питания или особого подхода, – не причина отказываться от участия в Летней Школе, мы просим лишь заранее известить организаторов о подобных нюансах!
В этом году Летняя Школа вновь проводилась в учебно-оздоровительном комплексе «Лесное озеро» Финансового университета при Правительстве Российской Федерации. На территории комплекса расположены 2 жилых корпуса, медицинский корпус, соединенный с главным корпусом крытым отапливаемым переходом, 2 коттеджа, спортивные площадки различных направлений: мини-футбол, баскетбол, волейбол, большой теннис, множество зон отдыха с беседками.
Сам же комплекс раскинулся на берегу живописного Истринского водохранилища, что в 70 км от Москвы, в Солнечногорском районе.
Буст ваших знаний + здоровый отдых = Летняя Школа CTF 2023!
Заключение
Летняя Школа CTF – это проект, который делают Люди! Организаторы, спонсоры, партнёры грантов, транспортная и техническая команды, медиагруппа, спикеры, кураторы, наставники и сами участники – благодаря каждому из вас этот проект живёт, развивается и с каждым годом получает всё большие возможности для передачи бесценного опыта и знаний подрастающему поколению ИБ-специалистов. Вклад каждого имеет свой, особое значение для общего дела, и мы благодарим всех, кто принимал участие и помогал в организации Летней Школы CTF 2023!
Особую благодарность выражаем принимающей стороне - учебно-оздоровительному комплексу «Лесное озеро» Финансового университета при Правительстве Российской Федерации и лично ректору университета Прокофьеву Станиславу Евгеньевичу и его команде.
А также Всероссийскому общественному движению наставников детей и молодежи «Наставники России».
Кому сказать "спасибо" за Летнюю школу 2023?
За помощь в организации XI Летней Школы CTF 2023 Ассоциация руководителей служб информационной безопасности выражает благодарность спикерам, партнерам и всем неравнодушным людям и компаниям. Наше мероприятие состоялось благодаря Вам. Спасибо!
Отдельно благодарим за поддержку НАМИБ, Министерство цифрового развития, связи и массовых коммуникаций Российской Федерации и губернатора Подмосковья Андрея Воробьева.
Особую благодарность выражаем генеральному и официальному партнерам - RDP и Сбер.
Спасибо нашим партнерам за материальную и техническую поддержку.
Партнеры: Гознак, Координационный центр доменов .RU/.РФ, Лаборатория Касперского.
Партнеры грантов: Киберпротект, НТЦ «Вулкан», EdgeЦентр, «SearchInform», УЦСБ, «ИнфоТек», Код Безопасности, «Star Force», «White Hack», Positive Technologies, UserGate, T1 Watchman.
Генеральный информационный партнер: Хакер.
Информационный партнер: CTF News.
Технологические партнеры: ПАО «МТС», UserGate, компания «Актив Софт».
Особая благодарность за предоставление широкополосного Интернета команде компании МТС.
Транспортный партнер: ИАЦ «Борей».
Спасибо всем спикерам за ваши доклады и знания, которые увезли с собой наши участники!
Александр Молчанов, Александр Трунев, Алексей Гуляев, Андрей Масалович, Артем Избаенков, Артем Калашников, Вадим Михайлов, Виктория Елагина, Виталий Васюнин, Владимир Иванов, Владимир Черепанов, Глеб Марченко, Даниил Лобанов, Дмитрий Муковкин, Дмитрий Скляров, Евгений Царев, Евгений Широков, Ирина Слонкина, Людмила Нуйкина, Максим Подобаев, Никита Бекетов, Сергей Голованов, Татьяна Ширяева.
Отдельную благодарность выражаем всем, кто помогал нам в реализации проекта!
Александр Будников, Александр Меньщиков, Александр Смирнов, Александр Шойтов, Александра Троцкая, Алексей Гуляев, Алексей Посикера, Алексей Фомин, Алина Алексеева, Анастасия Дюмулен, Анастасия Пан, Анастасия Шишкова, Андрей Глухарев, Андрей Голов, Андрей Крутских, Андрей Масалович, Андрей Чахеев, Анна Балухта, Анна Коротышева, Антон Быков, Антон Марков, Арсений Ларченков, Арсений Палагин, Артем Калашников, Богдан Кондратьев, Вадим Михайлов, Вадим Ружников, Вероника Гаршина, Виктор Покусов, Виктория Бунчук, Виктория Сабурская, Владимир Иванов, Владимир Лось, Вячеслав Новиков, Галина Козырева, Глеб Сердитых, Григорий Остапенко, Даниил Лобанов, Данил Заколдаев, Денис Масленников, Денис Петровский, Дмитрий Богданов, Дмитрий Гусев, Дмитрий Муковкин, Дмитрий Федоров, Евгений Царев, Екатерина Сватова, Елена Федина, Елизавета Антонова, Иван Нагорнов, Игорь Душа, Игорь Захаренков, Игорь Макаров, Игорь Морозов, Ильназ Мустафин, Ипполит Дюмулен, Ирина Корх, Ирина Поздняк, Искандер Зулькарнеев, Искандер Зулькарнеев, Кристина Сауберг, Ксения Харламова, Леонид Ротков, Максим Куликов, Максим Марушкин, Максим Подобаев, Марина Шутова, Михаил Кадер, Наталья Михайленко, Никита Полуэктов, Николай Микрюков, Оксана Полякова, Олег Иевлев, Олег Томниковский, Ольга Баскакова, Ольга Горлова, Ольга Карпунина, Павел Горбачев, Рустам Хидиятуллин, Саркис Шмавонян, Сауле Аманжолова, Сергей Будников, Сергей Волков, Сергей Голованов, Сергей Горелик, Сергей Коношенко, Сергей Лебедь, Сергей Ожегов, Сергей Сухман, Сергей Ширяев, Станислав Шевченко, Татьяна Ровенская, Элина Яруллина, Юлия Бахмутова, Юлия Черникина, Юрий Багров, Юрий Рожнов.
Спасибо команде организаторов Летней школы за всю проделанную работу!
Александр Котов, Александра Мартынова, Алексей Гуляев, Алексей Овчинников, Алиса Соболева, Антон Зеунов, Арина Казанцева, Валерия Кириллова., Виктор Минин, Галина Котлова, Даниил Лобанов, Даниил Ширшов, Евгений Емельянов, Елизавета Антонова, Иван Краснопольский, Кирилл Минин, Лев Хакимов, Максим Подобаев, Максим Смирнов, Маргарита Карева, Маргарита Рублева, Наталия Бекасова, Наталья Мануйлова, Никита Бекетов, Сергей Кузнецов.
Благодарим членов Ассоциации руководителей служб информационной безопасности (АРСИБ) за активное участие в нашем мероприятии!
Александр Мишурин, Александр Першин, Алексей Подмарев, Андрей Нуйкин, Артем Избаенков, Владимир Бугров, Дмитрий Костров, Илья Алексенко, Марат Шамсудинов, Мария Худышева, Михаил Смирнов, Ольга Курбанова, Сергей Голяк.
Источники:
«Летняя Школа CTF 2023»: итоги | ACISO CTF | Дзен
Кому сказать "спасибо" за Летнюю школу 2023? | ACISO CTF | Дзен
C 30 июля по 9 августа 2021 года в шале-отеле «Таежные дачи» в Звенигороде прошла очередная традиционная Летняя школа CTF. В течение 11 дней участники прошли курс, состоящий из ежедневных лекций от экспертов в области информационной безопасности, представителей крупных IT-компаний и участников топовых CTF-команд. Лекционный материал сопровождался ежедневной практикой с решением разных типов задач по программированию и ИБ. По вечерам после учебы – отдых или развлекательные мероприятия от организаторов.
Организация мероприятия проходила следующим образом: до начала Летней школы участники прошли тест для определения уровня знаний. По результатам теста организаторы распределили участников по командам, во главе которых назначили кураторов. Всего было 12 команд, состоящих из учеников с разным уровнем знаний.
В этому году Летнюю школу посетило 87 участников из разных регионов России и СНГ, таких как: ЦФО, ДВО, Санкт-Петербург, Екатеринбург, Новосибирск, Ярославль, Сургут, Воронеж, Донецк, Таганрог, Томск, Пенза, Магнитогорск, Петрозаводск, Снежинск, Краснознаменск.
«Как организаторы, мы старались сделать так, чтобы ученики на Летней школе получали не только полезные технические знания, но и как можно больше знакомились и общались друг с другом, потому что командная работа и умение находить общий язык крайне важная составляющая успешной CTF-команды и полезный навык для любого специалиста. Для этого мы делали досуговые командные активности с рандомным распределением и по тому же принципу расселяли участников по номерам», – так описала свой подход к Летней школе команда организаторов.
Лекции на Летней школе читали представители таких компаний, как: ServicePipe, Лаборатория Касперскоrо, Код Безопасности, ЦФТ, НКЦКИ, издательство Хакер.ру, КриптоПРО, Group-IB, Инфорус, Cisco, Сбер, SearchInform, Актив-софт, ОМП, PassWare, Digital Security, ООО «Сеть Партнерств», Security Intelligence Cryptocurrencies Platform, Хакердом, Ассоциация руководителей служб информационной безопасности (АРСИБ) и другие.
Практическая часть состояла из ежедневных тасков, лабораторных на проведение тестирования на проникновение, лабораторной работы по компьютерным сетям и системному администрированию, хакатона «Сервис поиска фишинговых сайтов», тренировки Attack-Defense от команды Хакердом и AntiCTF, где участникам предстояло написать свои собственные таски, которые после проверки и модерации от технической группы давались для решения другим участникам. Также в один из дней проводилась секция от Георгия Кигурадзе для учеников с продвинутым уровнем знаний в обратной разработке. Чтобы попасть на секцию, участникам необходимо было пройти дополнительный отбор перед началом Школы.
За решение практики участникам начислялись баллы в два зачета: командный и индивидуальный. В конце Летней школы команды и участники, набравшие наибольшее количество баллов, награждались призами от спонсоров.
Досуговые мероприятия состояли из, караоке, спортивных игр, игр «Что? Где? Когда?», «Своя игра» и «Угадай мелодию», фестиваля красок Холи и прощального костра с «обнимашками». Дополнительной досуговой активностью стала игра «Киллер», цель которой – познакомиться с как можно большим количеством людей и придумать тактику игры, чтобы получить информацию для выполнения задания.
В последний день прошел фестиваль красок «Холли» и флешмоб «День Российского флага».
Финальное мероприятие Летней Школы – прощальный костер и «Обнимашки», флешмоб, на котором участники говорили друг другу теплые слова и повязывали памятную ниточку на специальное ожерелье. В последний день прошло официальное закрытие смены, награждение участников по итогам успеваемости и обед с праздничным тортом.
Источник: Всё о CTF в России
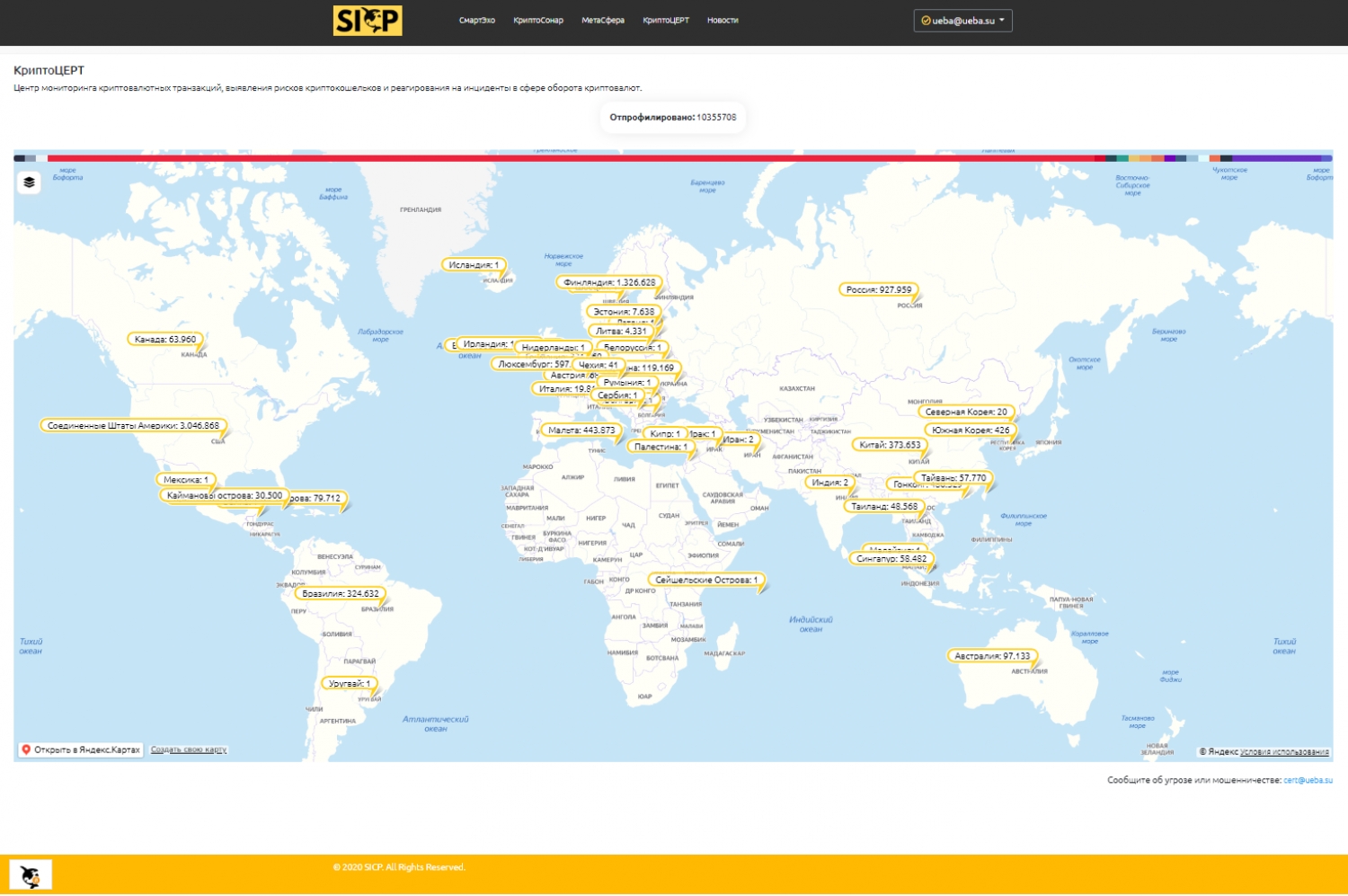
On July 30, the SICP (Security Intelligence Cryptocurrencies Platform) platform announced the launch of the first Russian commercial Center for monitoring cryptocurrency transactions, identifying the risks of cryptocurrency wallets and responding to incidents in the field of cryptocurrency circulation (CryptoCERT).
This service is the first in Russia and the UIS. Today, any citizen or organization can send information about fraud (another threat or risk) related to cryptocurrencies. Additionally, the publicly available interactive map displays profiled crypto wallets by country. The custom menu allows you to display one or more profiles. The legend displays the share and number of wallets associated with the profile. For registered and verified users, a wider visualization functionality is available.
It should be noted that on July 22, the State Duma of the Russian Federation adopted in the 3rd reading the law "On digital financial assets". The new rules will enter into force on January 1, 2021. The law "On digital currency" is expected to be considered in the coming autumn.
Remarkably, today is World Day Against Trafficking in Persons. It is a serious crime and gross violation of human rights. The United Nations Office on Drugs and Crime (UNODC), as the guarantor of the United Nations Convention against Transnational Organized Crime and the Protocols thereto, assists States in their efforts to implement the Trafficking in Persons Protocol.
By the way, this factor is taken into account when assessing the risks of crypto wallets, in the SmartEcho service, and identifying suspicious transactions ...
Source: sicp.ueba.su
Source: k4y0t.ru
QUARANTINE CHIMERAS: CYBER FRAUDSTERS CREATE A SYSTEM OF FAKE PASSES
Written by Bederov IgorUsing the new scheme, fraudsters plan to steal money and passport data, gain access to accounts on social networks and electronic mailboxes of Russians who needed to issue passes during the quarantine period. At the moment, criminals are working on creating clones of government agencies responsible for issuing documents (including mos.ru, mosreg.ru and gosuslugi.ru), and fake media portals on which it is planned to post fake news, experts told Izvestia on cybersecurity. In addition, the planned hackers and the mass mailing of messages via e-mail, social networks and instant messengers. To protect against intruders, experts advise using information verification services. About how to do this - in the material of Izvestia.
Clone attack
Forced isolation due to the COVID-19 pandemic is forcing people to spend more and more time on the Internet. The network is needed for working remotely, studying, ordering goods and organizing home leisure activities. The growth of traffic was even confirmed by the deputy head of the Ministry of Communications Alexey Volin, who said that "when they stayed at home, the people rushed to the Internet, and rushed there with terrible force."
According to the Russian company "Internet Rozysk", network scammers also decided to take advantage of the trend. Now they are organizing a global criminal system consisting of fake sites, hacked accounts on social networks and malicious Telegram bots. Criminals are going to attract people with a service to provide passes for moving around the city in the context of the COVID-19 epidemic, and then steal their money and personal data.
“We got information about the upcoming action using our bots, which are embedded in the darknet (the shadow segment of the Internet. - Izvestia) and a number of closed chats,” said Igor Bederov, CEO of the company. “We learned from them that a scheme is being prepared for deceiving people who plan to obtain passes for themselves.”
According to the expert, this scheme, known as the “rabbit hole”, involves the mass mailing of addresses of fake sites that will be as similar as possible to the resources of government agencies with the authority to issue documents (including mos.ru, mosreg.ru and gosuslugi.ru ) It is expected that this will happen with the help of hacked accounts on social networks and Telegram bots. Attackers will try to confirm the legitimacy of the messages with links to articles allegedly posted in leading Russian media - their sites will also receive clones.
Throughput pressure
After users switch to malicious resources, they will be asked for passport data for issuing passes, as well as bank card details - supposedly to pay for the service upon receipt.
“Their further actions can be predicted from earlier criminal actions of this type, which, in particular, were conducted under the guise of receiving certain compensatory state payments or paid bank surveys,” warned Igor Bederov. - Then the criminals, as a rule, sought a voluntary transfer of money, after which they managed to withdraw the remaining funds from the cards with the help of the details already received.
At the same time, personal data of users is likely to become goods for sale on the black market, forming new illegal bases. The final stage of the scheme is usually the hacking of the personal accounts of the deceived user on social networks and his mailboxes (this is done using the captured cookies), after which they are connected to the distribution of malicious messages.
The large-scale nature of the illegal action was confirmed by specialists of the Security Intelligence Cryptocurrencies Platform (SICP) risk analysis service.
“The scale of the new threat is comparable to the financial pyramids, the organizers of which spend huge sums on promotion through famous people and popular sites,” said Aleksandr Podobnykh, an independent expert at SICP. - And the state’s symmetric response to this, I’m afraid, can only be a significant increase in control over SIM cards, hosting and data centers.
According to experts, in addition to the already mentioned increase in Russian Internet traffic, there are a number of additional factors that will play into the hands of criminals, increasing their chances of success.
“First of all, they include neurotization of people against the background of the epidemic, which makes it easier to manipulate,” said Luka Safonov, director of the information security department of the National Engineering Corporation. - On the other hand, the situation is complicated by the situation with state portals, which now do not withstand the influx of visitors. The fact is that when people cannot get a pass through an official resource, they are most likely to be interested in an alternative offer.
Simple calculations
Despite the sophistication of criminal methods, you can still protect yourself from fraud using a few simple tools that allow you to calculate fraudsters. The instruction for checking incoming messages to Izvestia was provided by Internet Rozysk:
- all state organizations and private companies operating in Russia have domain names registered in our country. Therefore, suspicious links should be checked through the WHOIS service, which reveals their true owners. If, according to the results of the examination, they turn out to be hidden, then it is better not to trust the received information.
- checking the sender of the letter, which can be carried out through the verifiers of mailboxes located on the sites https://2ip.ru/mail-checker/, will be useful in such a situation; http://ru.smart-ip.net/check-email/ and https://ivit.pro/services/email-valid/. It will make sure that the message came from the server of the organization whose employees were indicated as its authors.
- also an indirect sign of fraud can be the so-called shortened link, which has the end click.ru, goo-gl.ru, etc. Its original address is also worth checking (without going to it!) Using special services - they are available at: https://scanurl.net/; https://vms.drweb.ru/online/, https://virusdesk.kaspersky.ru/ and https://iplogger.ru/url-checker/.
The Izvestia source in the power structure confirmed the need for additional verification of the legitimacy of the request when receiving a request for the transfer of funds. “This needs to be done even if it seems that the message was sent to one of the state structures,” he noted.
The expert also proposed an additional way to check emails received via e-mail: you should try to reply to a suspicious message. If the address of the organization’s employee does not change, then with a high degree of probability it is not fake.
However, this does not eliminate the need for additional checks described in the instructions.
Roskomnadzor responded to a request from Izvestia that they were ready to promptly send administrators of sites hosting false information notifications of the need to delete it, if the Prosecutor General's Office so requires.
“If this instruction is not followed, information will be communicated to telecom operators about the need to limit the access of Russian users to this content,” the organization noted.
At the same time, Roskomnadzor emphasized that they do not have the authority to conduct investigations to prevent cybercrime and fraud on the Internet.
Izvestia also sent inquiries to the Ministry of Internal Affairs, the FSS and the Moscow Department of Information Technology. However, operational responses could not be obtained.
Source: IZ.ru
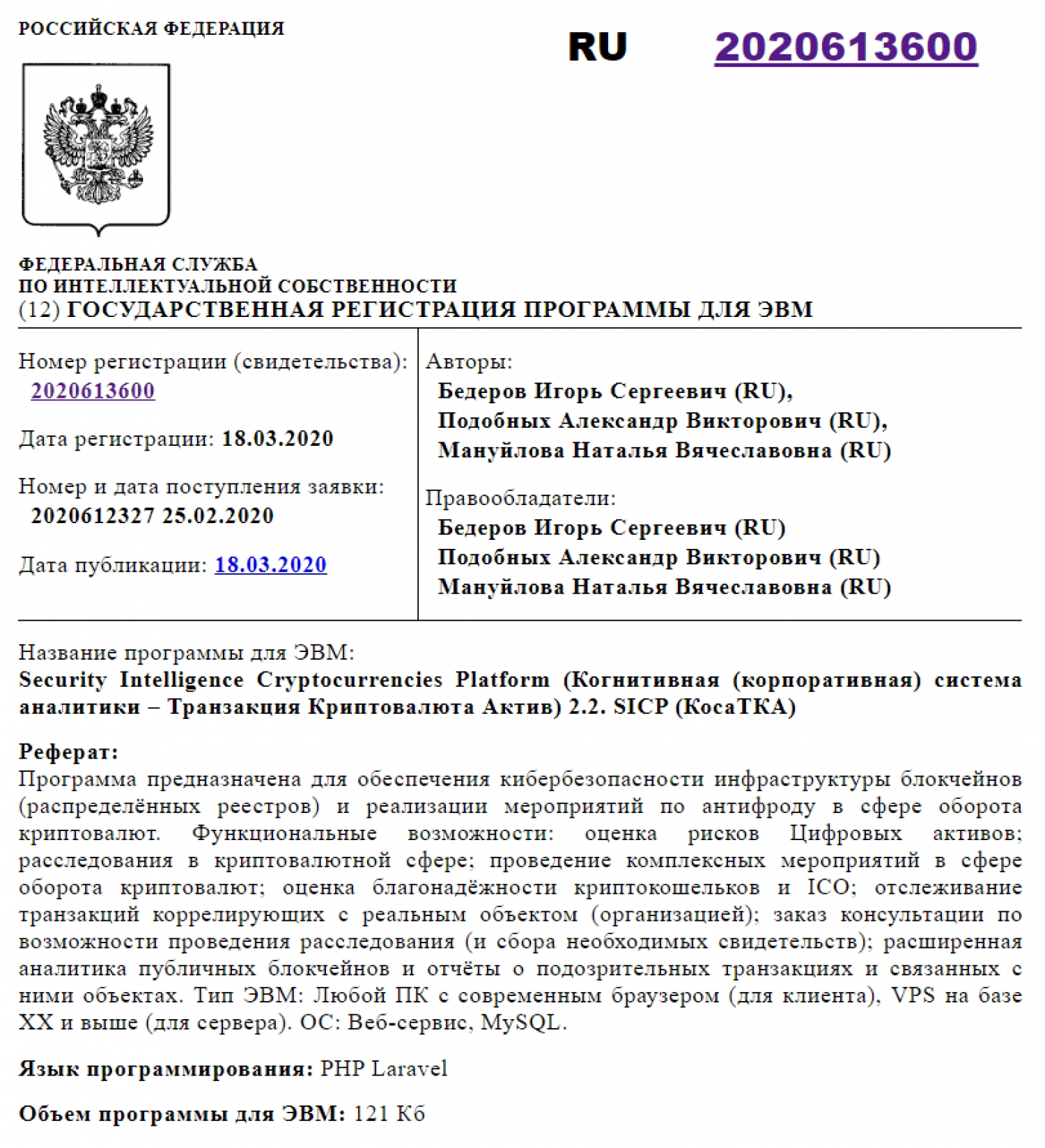
SICP PASSED STATE REGISTRATION IN THE FEDERAL SERVICE FOR INTELLECTUAL PROPERTY OF THE RUSSIAN FEDERATION
Written by Aleksandr PodobnykhThe quarantine situation causes the rapid development of distance services, as well as the widespread use of contactless payments and electronic currencies. At the same time, a significant event took place on the Russian cryptocurrency market. A few days ago, the SICP platform team received a notification from the Federal Intellectual Property Service of the Russian Federation about the state registration of a computer program (03/18/2020 No. 2020613600) - Security Intelligence Cryptocurrency Platform (SICP) or Cognitive (corporate) analytics system Transaction Cryptocurrency Asset.
The platform’s web services are designed to provide cybersecurity for the infrastructure of blockchains (distributed registries) and implement anti-fraud measures in the field of cryptocurrency circulation. Functionality: risk assessment of Digital Assets; cryptocurrency investigations; conducting complex events in the field of cryptocurrency circulation; cryptocurrency wallet and ICO reliability assessment; tracking transactions correlating with a real object (organization); ordering advice on the possibility of an investigation (and the collection of necessary evidence); Advanced analytics of public blockchains and reports on suspicious transactions and related objects.
Today, a large number of SICP users leave user ratings about crypto-wallets and transactions, researchers actively use the SmartEcho and CryptoSonar services to evaluate crypto-wallets and visualize research (investigation) scenes, experts use CryptoSonar and MetaSphere services to save scenes and analyze the wallet and transaction pool (by internal tags).
In your personal account, verification tools are available for owners of crypto-wallets and even crypto-firms, with obtaining the appropriate status (and the ability to share certificates on social networks and on sites). There is the possibility of monitoring wallets for incoming / outgoing transactions (other events), saved scenes and functionality for conducting joint investigations (by registered users).
It is noteworthy that it is on Cosmonautics Day that we will announce this event! .. A significant step, if not for the entire global financial and technological sector, then surely for the entire industry of end-to-end technologies...
Source: K4Y0T Project.
SPECIAL ELABORATIONS DEPARTMENT AT TECHNOPARK OF ST. PETERSBURG IS PRESENTED FOR INFINITY GROUP
Written by Aleksandr PodobnykhOn September 3, 2019, in St. Petersburg, specialists and residents of the SafeNet RIC of the St. Petersburg Technopark, together with the Russoft NP and Bee Pitron, held a presentation session for the Indian delegation of Infinity Group. The key focus of the event was the creation of a platform for interaction between participants in the Russian-Indian market.
As part of the meeting, Igor Bederov presented the developments of the Special Development Department for a distinguished guest from India. Mr. Darbari drew particular attention to existing developments in the field of cryptocurrency transaction control and crime prevention. According to him, in India, up to 20% of the population and a significant amount of low-level crime use cryptocurrencies. In addition, the country has not resolved the problem of relapse in previously convicted criminals.
Back in July, in the format of the Second Russian-Indian strategic dialogue, in order to establish a technology transfer, an agreement was signed between RUSSOFT and Infinity Group. As a result, the ICT Center of Excellence project was launched in India, designed to establish cooperation between the two countries in the direction of business development and international assistance to SMEs.
The delegation of the Infinity Group, headed by Mr. Darbari, flew to Russia to meet with potential recipients of investments and to transfer technology from Russia to India under the “Made in India” program.

After a tour of the engineering center, SafeNet residents presented their projects in the areas of Artificial Intelligence, Internet of Things, cyberphysical security, blockchain, virtual and augmented reality. The parties discussed the situation on the international high-tech market and considered options for potential mutually beneficial cooperation. ICT experts emphasized the relevance of Russian solutions to the market of India and other countries and discussed the possibility of implementation.
Source: Engineering center SafeNet.
CYBERPOL PUBLIC SEARCH CRIMINAL DATABASE TO INCLUDE CRYPTOCURRENCY WALLETS USED IN CYBERCRIME
Written by Aleksandr PodobnykhBRUSSELS, 1000, BELGIUM, June 18, 2019. CYBERPOL Public Search Criminal Database to include Crypto Currency wallets used in cyber crime.
CYBERPOL The International Cyber Policing Organization established by decree no WL 22/16.595 established today four years ago in Brussels made available to the public the first cyber criminal database empowered by the "Neural symbiotic network of the super computer" as the international cyber utility agency leader in investigation in cyber crimes and terror of the Dark-Web today.
This first Cyber Criminal Public Record Database in Beta Test mode currently will allow four basic levels of searching of wanted cyber criminals allowing for verification and searches of IP's, emails and Cryptocurrency wallets used in on-line scams related to cyber crimes listed in the database.
In addition to this, all cryptowallets using crypto currencies in cybercrime will now be listed on the Cyber Crime search engine by CYBERPOL organization making it very difficult for cyber criminals to use crypto-currencies as payment methods for scams and cyber crimes.
You can now report any scam email to CYBERPOL that when verified will be listed in the CYBERPOL Cyber Criminal Public Database open to public to search.
More than £108,000 in bitcoin was paid by victims of the WannaCry ransomware attacks using bitcoin as undetectable crypto-currency payment. Since such wallets used in crimes are not considered privacy breaches but in the interest of the law it is in the public interest to warn public and make such wallets black listed public records globally before further victims falls pray to cyber crimes Baretzky President of CYBERPOL said.
Public and law enforcement can use this CYBERPOL facilities for free and report such e-mail of extortion to be entered into the public records of CYBERPOL Public Utility directly by requests.
Several entries is already public to search on-line and don't try to fool CYBERPOL. The tracking of cyber crimes goes the extra mile to track the same hackers when visiting the search engine on CYBERPOL website using a new AI (Artificial Intelligence) named 666 to capture both mac and serial number of such computers. Don't be a hackers fool to search yourselves if you are already involved in cyber crimes, the CYBERPOL Spokes Person warned.
This will be a huge blow for crypto currencies and wallets used in cyber crimes and scams as the wallet numbers will be public listed and open to see to all public and law-enforcement free of charges in disrupting cyber crimes.
The message is clear and simple President Ricardo Baretzky of CYBERPOL said "Don't use any Crypto Currencies in INTERNET crimes as we will not only find you but list your crypto WALLET accounts for good in the block-chain based search engine of CYBERPOL Supper Computer AI 666 symbiotic neural network and let me assure all those financial criminals, once listed there is no escape! I hope this message is clear to criminals and corruption".
It seems the days messing with elections using secret corruption payments could be counted as CYBERPOL has set a new paradigm in combating cyber crimes and global corruption never seen before...
Source: EIN Presswire.
ANNOUNCED THE CREATION OF A SPECIAL ELABORATIONS DEPARTMENT
Written by Aleksandr PodobnykhIn early July, SafeNet regional engineering center (structural division of JSC Technopark of St. Petersburg) has introduced a new project.
Thus, together with the company Internet-Rozysk was announced the creation of the Special elaborations department. Which purpose is the organization of work with information and analytical and other products intended for the prevention, suppression and investigation of the offenses committed by means of information and telecommunication technologies.
Key activities of the new Department:
1. interaction with profile startups, companies and developers;
2. organization of interaction with state and law enforcement agencies. Control over the legality and legality of the development;
3. consulting and carrying out examinations, development of methodical and scientific base, training and professional development for the persons engaged in law enforcement activity, and also other persons;
4. organization of demonstration zones, exhibitions, interaction with the media, negotiations aimed at attracting interest in the development of the Department, the implementation of its product line, promotion of activities.
Developers engaged in the following project categories are invited to interact:
- assessment of reliability of contractors and staff;
- non-instrumental lie detection;
- detection of illegal activities in social networks;
- analysis and tracking of cryptocurrency transactions;
- establishing users phone numbers and email addresses;
- establishing users of secure messengers;
- enrichment and analysis of large amounts of publicly available data;
- detection and suppression of confidential information leaks;
- darknet Analytics;
- analysis and decoding of Internet traffic.
Source: SafeNet еngineering center.
More...
SENTINEL PROTOCOL LAUNCHES THE INTERACTIVE COOPERATION FRAMEWORK API
Written by Aleksandr PodobnykhSolution to protect crypto assets by fighting fraud, scams, and malicious threats.
Singapore, 29 October 2018 — Sentinel Protocol announces the launch of the Interactive Cooperation Framework API (ICF API). After the successful launch of the UPPward Chrome Extension, a crypto scam protection solution, Sentinel Protocol continues to lead the crypto security industry by arming crypto exchanges and wallet services with its ICF API.
The new ICF API is designed to be integrated with financial software applications to proactively protect crypto assets belonging to organizations and clients from malicious threats. Before completing a transaction, the ICF API enables a financial application to query Sentinel Protocol’s Threat Reputation Database (TRDB) and check whether or not a specific crypto wallet address, URL, domain, or Telegram ID is safe. Within milliseconds, the TRDB sends a response. Depending on the type of response, a pending transaction can be immediately rejected and terminated; an alert or warning could be generated; or the transaction could be allowed if the alert level is low.
The key features of the ICF API are:
- Platform agnostic — can be used by any exchange, wallet, DApp, or application.
- Online access to collective security intelligence data held in the TRDB.
- Validated whitelists and blacklists of crypto wallet addresses, URLs, and domains related with malware, phishing, and scams.
While blockchain’s core technology has earned an excellent reputation for strong security, cryptocurrency assets continue to be stolen on a daily basis. Crypto exchanges and wallet services today have limited capabilities for preventing users from accepting or sending crypto funds to malicious addresses or for identifying malicious URLs associated with phishing and malware.
To address the above needs, the ICF API beta version will be made available to organizations by the end of October for testing and evaluation. The full production version will be deployed in early 2019.
Sentinel Protocol, is the world’s first crowd-sourced threat intelligence platform utilizing the advantages of decentralization to protect cyberspace with blockchain security. It aims to equip individuals and organizations with cybersecurity solutions that protect their valuable cryptocurrency assets from malicious threats, attacks, and fraud. Sentinel Protocol is headquartered in Singapore and has offices in Seoul, South Korea and Tokyo, Japan.
Source: Medium.
NEURAL NETWORK LABORATORY OF THE PHYSTECHPARK WILL SAVE THE BLOCKCHAIN FROM CRIME
Written by Aleksandr PodobnykhIn the Moscow region raised the Auditor blockchain. Thus, the Center of Neuroinnovations, formed with the support of the Rating agency for the evaluation of digital economy projects at Plekhanov University, and the expert-analytical platform “Smart country” (resident of the Phystechpark in Dolgoprudny) announced the launch of the project under the working name Neuro Auditor Blockchain (NeuroB) — which is an artificial intelligence, focused on the fight against fraudulent schemes of fashion technology ICO.
The project will minimize the losses of investors in the blockchain sector, which currently amount to more than $ 9 million per day...
This is a platform based on neural calculations to identify unscrupulous blockchain projects, a kind of Auditor. That is, Scam (fraud) can be shot back on the approach of high-tech guns, and investors will not lose money. The most important task of the project, according to the businessman, to return to ordinary investors in cryptonomicon.
Since the beginning of 2018, 537 ICO have been registered for a total amount of $ 13.7 billion. For comparison, in 2017, 552 ICO were held with the volume of attracted funds of only $ 7 billion. Also, compared to last year, the average ICO size almost doubled: from $ 12.8 million to more than $ 25.5 million...
Source: Hi-tech News.
Waves Ecosystem Comes To Your Browser. Waves has launched an extension to securely sign transactions. Now it is even more convenient to purchase token SICP.
The new Waves Keeper browser extension turns your browser into a keychain that enables you to sign transactions securely on third-party web resources without entering your seed or password. So now, if a Waves-integrated website or dApp requires you to sign a transaction, you can do it with just a couple of clicks, right in your browser.
This is the first version of the browser extension, which currently works only in Google Chrome. In forthcoming releases they are planning to extend its functionality and develop a cross-browser solution, available for all popular browsers.
Source: blog Waves Platform.
О КОСАтка
Корпоративная система аналитики Транзакция Криптовалюта Актив - кибербезопасность инфраструктуры блокчейнов и антифрод в криптовалютной сфере (антискам, прозрачность, комплаенс).
Связаться
Российская Федерация, Москва
Тел.: +7 (911) 999 9868
Факс:
Почта: cosatca@ueba.su
Сайт: www.ueba.su